Taller Reversing .exe
https://www.youtube.com/channel/UCPNPSP20z4FGfgMJ71VOJjw/videos
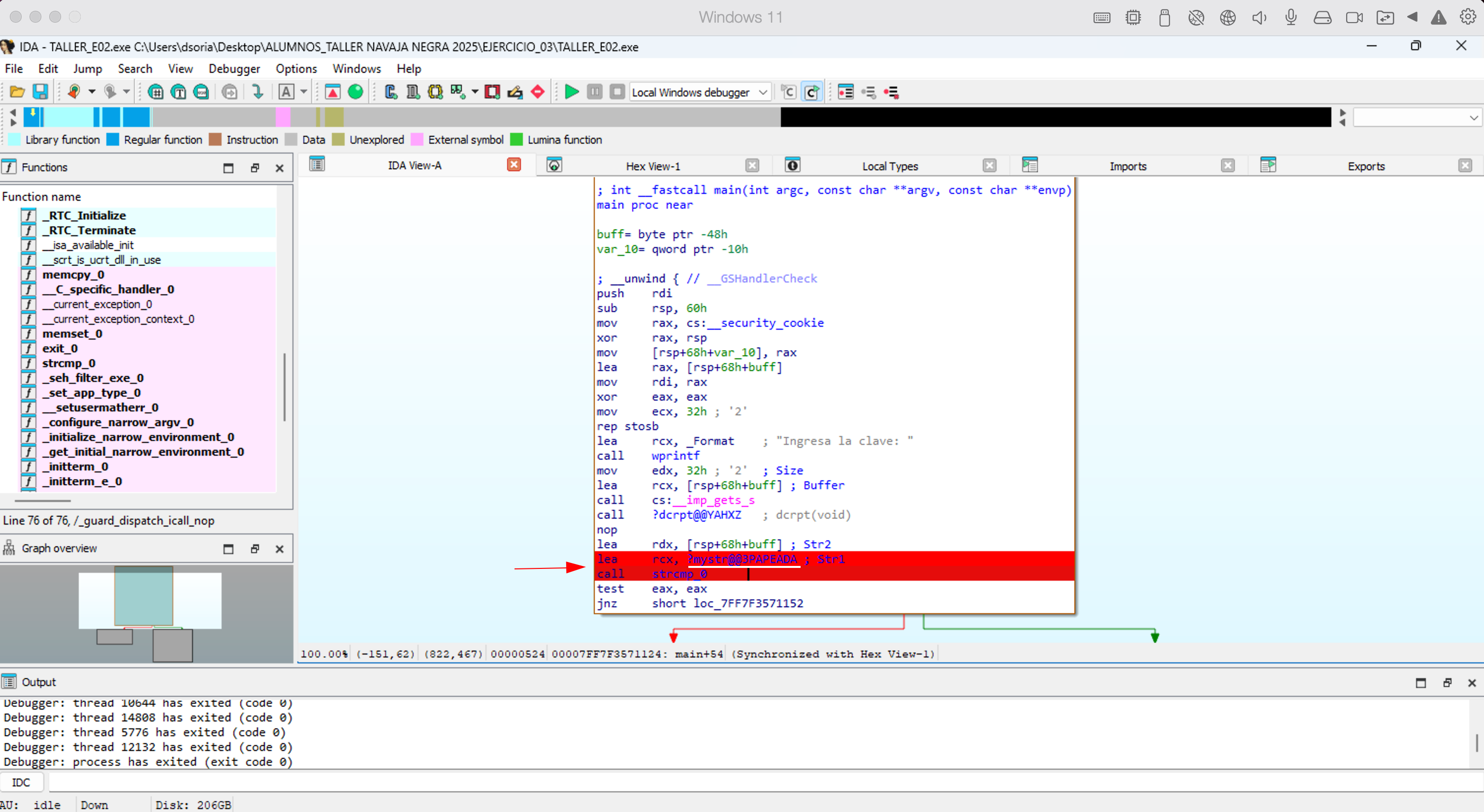
; int __fastcall main(int argc, const char **argv, const char **envp)
main proc near
result= byte ptr -58h
access_key= byte ptr -50h
var_18= qword ptr -18h
; __unwind { // __GSHandlerCheck
push rdi
sub rsp, 70h
mov rax, cs:__security_cookie
xor rax, rsp
mov [rsp+78h+var_18], rax
lea rax, [rsp+78h+access_key]
mov rdi, rax
xor eax, eax
mov ecx, 32h ; '2'
rep stosb
lea rcx, _Format ; "Ingrese la clave de acceso: "
call printf
mov edx, 28h ; '(' ; Size
lea rcx, [rsp+78h+access_key] ; Buffer
call cs:__imp_gets_s
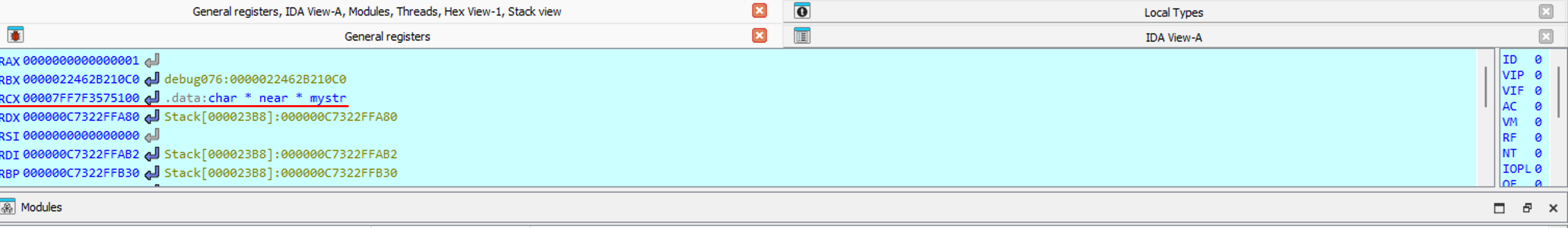
lea rcx, [rsp+78h+access_key] ; serial
call ?myfuncion@@YA_NPEAD@Z ; myfuncion(char *)
mov [rsp+78h+result], al
movzx eax, [rsp+78h+result]
test eax, eax
jz short loc_140001107
Tecla X para ver sus usos
jz → (if)
canary → security code (C++)
call cs:__imp_gets_s → lee teclado por entrada
EJ3
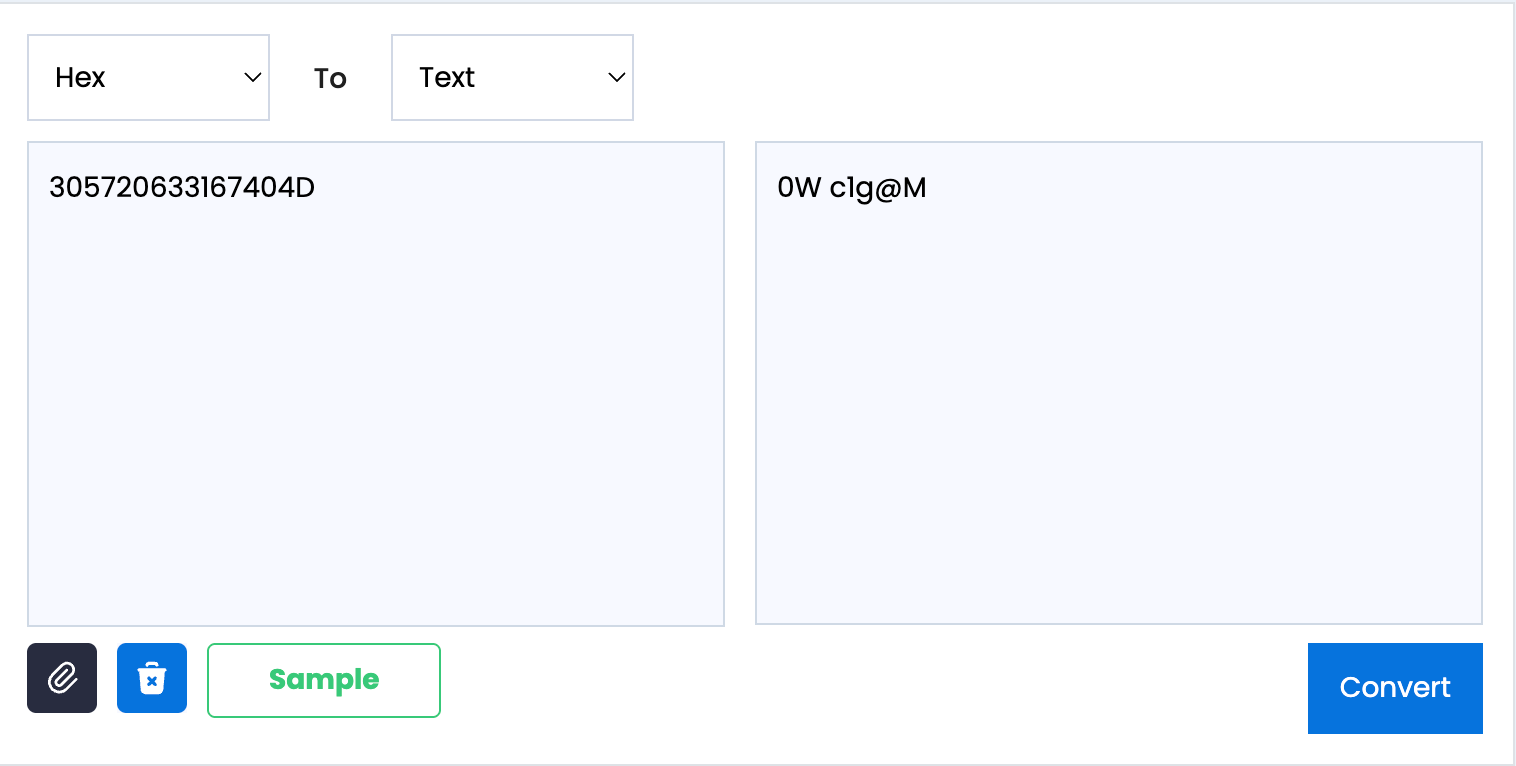
El 4
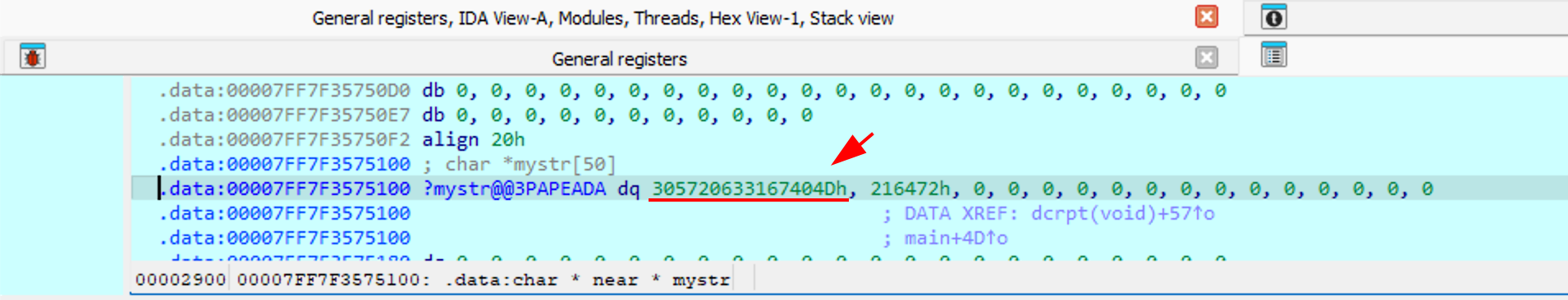
cada letra que pone se va sumando en hexadecimal. y luego se pone en decimal